Scrivener research paper dissertation workflow chart.
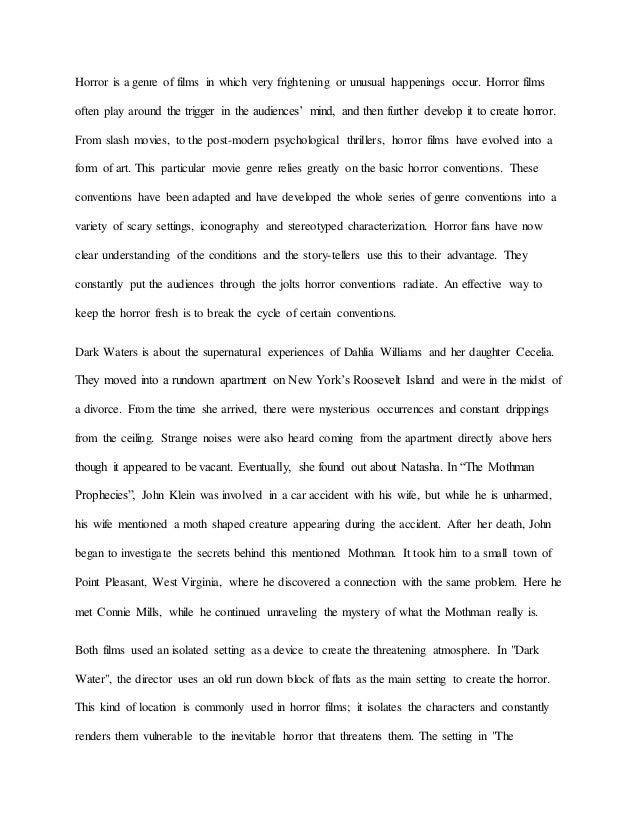
The accuracy rate of the K-nearest method in Waledac detection is relatively low but the accuracy rate of the SVM method in Waledac detection is only 89.2%. According to the comparison results, the REP tree algorithm has better detection results and the accuracy rates for the Waledac and Storm botnet are up to 97%. Black Energy uses basic encryption technology to make the executable file.
Analysis and Detection System (BADS) framework for detecting Botnet. The BADS framework has been used as a guideline to devise the methodology, and we divided this methodology into six phases: i. data collection, customization, and conversion, ii. feature extraction and feature selection, iii. Botnet prediction and classification, iv. Botnet detection, v. attack notification, and vi. testing.
The threat landscape is constantly changing. Stay on top of the latest trends that matter to you with our interactive security insights. Our threat researchers are sharing new data every month. We’ve been publishing threat intelligence reports for well over a decade. In that time, we’ve.
Wireshark is a network protocol analyzer, and is the standard in many industries. It is the continuation of a project that started in 1998. Hundreds of developers around the world have contributed.
ZDNet's technology experts deliver the best tech news and analysis on the latest issues and events in IT for business technology professionals, IT managers and tech-savvy business people.
The only really visible end-goal of Conficker was the tried-and-tested method of monetizing large-scale malware infections; installing affiliate-program provided scareware that pays the affiliate for each successful purchase, and also installing the Waledac botnet, which was used to send out email spam, another way to make money out of large, successful botnets. I'd like to direct people to.
InformationWeek.com: News analysis and commentary on information technology trends, including cloud computing, DevOps, data analytics, IT leadership, cybersecurity, and IT infrastructure.